
Bitcoin mining is the process of verifying bitcoin transactions and recording them in the public blockchain ledger. In blockchain, the transactions are verified by bitcoin users, so basically the transactions have to be verified by the participants of the network. Those who have the required hardware and computing power are called miners. We will talk more about them later, but the important concept to understand here is that there is nothing like a centralized body—a regulatory body, a governing body, a bank—to make bitcoin transactions go through.
Any user with mining hardware and Internet access can be a participant and contribute to the mining community. The process is solved based on a difficult mathematical puzzle called proof of work. The proof of work is needed to validate the transaction and for the miner to earn a reward. All the miners are completing amongst themselves to mine a particular transaction; the miner who first solves the puzzle gets the reward. Miners are the network participants who have the necessary hardware and computing power to validate the transactions.
To understand bitcoin mining, you have to first understand the three major concepts of blockchain. In the bitcoin network, as mentioned, users called miners are trying to solve a mathematical puzzle. The puzzle is solved by varying a nonce that produces a hash value lower than a predefined condition, which is called a target. As of today, Bitcoin miners who solve a puzzle get a reward of Once a block is added to the blockchain, the bitcoins associated with the transactions can be spent and the transfer from one account to the other can be made. To generate the hash, Bitcoin miners use the SHA hashing algorithm and define the hash value.
If it is less than the defined condition the target , then the puzzle is deemed to be solved.
How Does Bitcoin Mining Work?
If not, then they keep modifying the nonce value and repeat the SHA hashing function to generate the hash value again, and they keep doing this process until they get the hash value that is less than the target. To do that, what would the steps be? First, transaction data is shared with bitcoin users from the memory pool. The transaction sits in an unmined pool of memory transactions. In a memory pool, unconfirmed transactions wait until they are verified and included in a new block.
Bitcoin miners compete to validate the transaction using proof of work. The miner who solves the puzzle first shares the result across the other nodes. Once the block has been verified, the nonce has been generated, then the nodes will start granting their approval. If maximum nodes grant their approval, the block becomes valid and is added to the blockchain. The miner who has solved the puzzle will also receive a reward of The 10 bitcoins for which the transaction was initiated now will be transferred from Beyonce to Jennifer.
In proof of work, a predefined condition the target is adjusted for every 2, blocks, which is approximately every 14 days. The average time to mine a block is 10 minutes, and to keep the time frame for block generation within 10 minutes, the target keeps adjusting itself. The difficulty of the puzzle changes depending on the time it takes to mine a block. This is how the difficulty of a block is generated: It is the hash target of the first block divided by the hash target of the current block. This is the difficulty being changed after every 2, blocks, so basically it is very hard to generate the proof of work—but it is very easy for the miners to verify once someone have solved the puzzle.
And once the majority of the miners reach a consensus, the block gets validated and added to the blockchain. What if someone tries to hack the data? Each block has solved a puzzle and generated a hash value of its own, which is its identifier. Now suppose a person tries to tamper with block B and change the data.
The data is aggregated in the block, so if the data of the block changes, then the hash value that is the digital signature of the block will also change. It will therefore corrupt the chain after it—the blocks ahead of block B will all get delinked, because the previous hash value of block C will not remain valid. For a hacker to make the entire blockchain valid for the block B that has been changed, he or she would have to change the hash value of all the blocks ahead of block B. This would require a huge amount of computing power and is next to impossible.
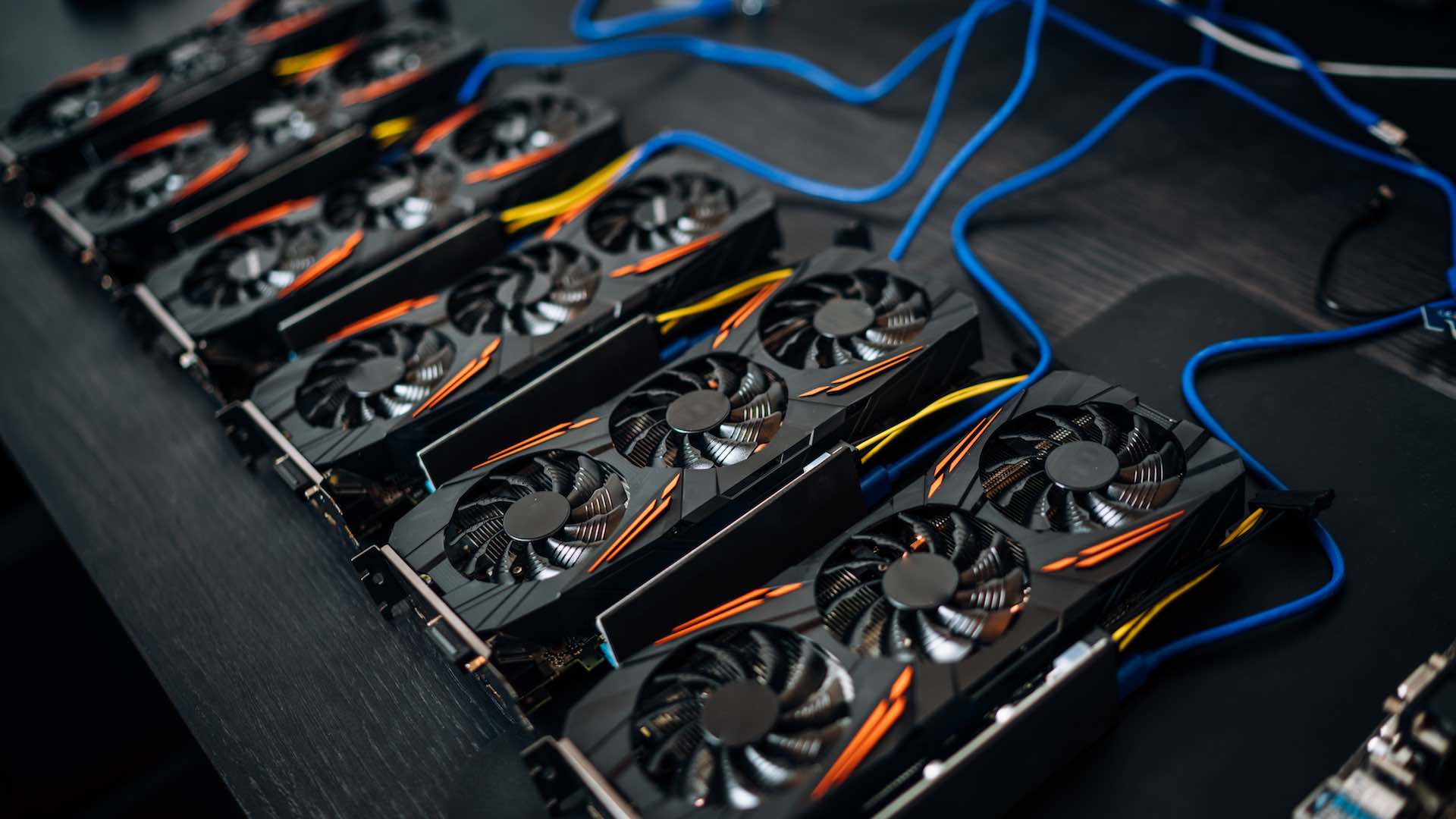
With this method, blockchain is non-hackable and prevents data modification. In the early days of bitcoin, miners used to solve the mathematical puzzles using regular processors—controlling processor units CPUs. It used to take a lot of time for mining Bitcoins and other cryptocurrencies, even though the difficulty levels were easier than today. As mentioned above, the difficulty level keeps changing and growing, so the miners also had to increase their processing power. They discovered that graphical processing units GPUs proved to be more efficient than regular CPUs, but this also had the drawback of consuming more electricity.
A miner has to calculate the return on investment based on the hardware and the cost of electricity and other resources needed to do the mining. Today miners use hardware called ASIC application-specific integrated circuit , which was specifically introduced for mining Bitcoin and other cryptocurrencies. It consumes less power and has a higher computing power. Miners are profitable when their cost of resources to mine one block is less than the price of the reward. So, Bitcoin miners use their resources hardware and electricity to verify a transaction, and each time a block is mined, new bitcoins are created in the network.
The total supply is limited to 21 million bitcoins; 17 to 18 million bitcoins have already been mined, so only 3 to 4 million are left. As of today, a reward of If individuals buy multiple lottery tickets and pool their tickets together, then this will increase their chances of winning. The bitcoin protocol includes several features that protect it against some of those attacks, such as unauthorized spending, double spending, forging bitcoins, and tampering with the blockchain.
Other attacks, such as theft of private keys, require due care by users. Unauthorized spending is mitigated by bitcoin's implementation of public-private key cryptography. For example; when Alice sends a bitcoin to Bob, Bob becomes the new owner of the bitcoin. Eve observing the transaction might want to spend the bitcoin Bob just received, but she cannot sign the transaction without the knowledge of Bob's private key. A specific problem that an internet payment system must solve is double-spending , whereby a user pays the same coin to two or more different recipients.
An example of such a problem would be if Eve sent a bitcoin to Alice and later sent the same bitcoin to Bob. The bitcoin network guards against double-spending by recording all bitcoin transfers in a ledger the blockchain that is visible to all users, and ensuring for all transferred bitcoins that they haven't been previously spent. If Eve offers to pay Alice a bitcoin in exchange for goods and signs a corresponding transaction, it is still possible that she also creates a different transaction at the same time sending the same bitcoin to Bob.
By the rules, the network accepts only one of the transactions. This is called a race attack , since there is a race which transaction will be accepted first. Alice can reduce the risk of race attack stipulating that she will not deliver the goods until Eve's payment to Alice appears in the blockchain. A variant race attack which has been called a Finney attack by reference to Hal Finney requires the participation of a miner. Instead of sending both payment requests to pay Bob and Alice with the same coins to the network, Eve issues only Alice's payment request to the network, while the accomplice tries to mine a block that includes the payment to Bob instead of Alice.
There is a positive probability that the rogue miner will succeed before the network, in which case the payment to Alice will be rejected.
How Does Bitcoin Mining Work?
As with the plain race attack, Alice can reduce the risk of a Finney attack by waiting for the payment to be included in the blockchain. Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that transaction. Ideally, merchants and services that receive payment in bitcoin should wait for at least one confirmation to be distributed over the network, before assuming that the payment was done.
- Mining Bitcoin with Nuclear Power;
- vibrate bitcoin.
- Mining Bitcoin with Nuclear Power | ScottMadden.
- Electricity needed to mine bitcoin is more than used by 'entire countries'.
Deanonymisation is a strategy in data mining in which anonymous data is cross-referenced with other sources of data to re-identify the anonymous data source. Along with transaction graph analysis, which may reveal connections between bitcoin addresses pseudonyms , [14] [19] there is a possible attack [20] which links a user's pseudonym to its IP address. If the peer is using Tor , the attack includes a method to separate the peer from the Tor network, forcing them to use their real IP address for any further transactions.
The attack makes use of bitcoin mechanisms of relaying peer addresses and anti- DoS protection.
Bitcoin network - Wikipedia
Each miner can choose which transactions are included in or exempted from a block. Upon receiving a new transaction a node must validate it: in particular, verify that none of the transaction's inputs have been previously spent. To carry out that check, the node needs to access the blockchain. Any user who does not trust his network neighbors, should keep a full local copy of the blockchain, so that any input can be verified. As noted in Nakamoto's whitepaper, it is possible to verify bitcoin payments without running a full network node simplified payment verification, SPV.
A user only needs a copy of the block headers of the longest chain, which are available by querying network nodes until it is apparent that the longest chain has been obtained.
Then, get the Merkle tree branch linking the transaction to its block. Linking the transaction to a place in the chain demonstrates that a network node has accepted it, and blocks added after it further establish the confirmation. While it is possible to store any digital file in the blockchain, the larger the transaction size, the larger any associated fees become. Various items have been embedded, including URLs to child pornography, an ASCII art image of Ben Bernanke , material from the Wikileaks cables , prayers from bitcoin miners, and the original bitcoin whitepaper.
The use of bitcoin by criminals has attracted the attention of financial regulators, legislative bodies, law enforcement, and the media. Senate held a hearing on virtual currencies in November Several news outlets have asserted that the popularity of bitcoins hinges on the ability to use them to purchase illegal goods.
A CMU researcher estimated that in , 4. Due to the anonymous nature and the lack of central control on these markets, it is hard to know whether the services are real or just trying to take the bitcoins. Several deep web black markets have been shut by authorities. In October Silk Road was shut down by U. Some black market sites may seek to steal bitcoins from customers. The bitcoin community branded one site, Sheep Marketplace, as a scam when it prevented withdrawals and shut down after an alleged bitcoins theft. According to the Internet Watch Foundation , a UK-based charity, bitcoin is used to purchase child pornography, and almost such websites accept it as payment.
Bitcoin isn't the sole way to purchase child pornography online, as Troels Oertling, head of the cybercrime unit at Europol , states, " Ukash and paysafecard Bitcoins may not be ideal for money laundering, because all transactions are public. In early , an operator of a U. A report by the UK's Treasury and Home Office named "UK national risk assessment of money laundering and terrorist financing" October found that, of the twelve methods examined in the report, bitcoin carries the lowest risk of being used for money laundering, with the most common money laundering method being the banks.
Securities and Exchange Commission charged the company and its founder in "with defrauding investors in a Ponzi scheme involving bitcoin".
- how much has bitcoin increased in the last 5 years!
- The history of Bitcoin.
- What is Bitcoin Mining and How Does it Work? ( Updated).
- The pandemic is turning fracking companies into Bitcoin miners.
From Wikipedia, the free encyclopedia. Peer-to-peer network that processes and records bitcoin transactions. For broader coverage of this topic, see Bitcoin. See also: Mining pool. Main article: Online transaction processing. For broader coverage of this topic, see Cryptocurrency and security. Main article: Darknet market.
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
 Mining bitcoin what is
Mining bitcoin what is
:max_bytes(150000):strip_icc()/BlockReward-5c0ad88946e0fb0001af7198.png) Mining bitcoin what is
Mining bitcoin what is
Related mining bitcoin what is
Copyright 2020 - All Right Reserved